NVIDIA OpenShell Is Now in 17 Enterprise Stacks — and the Agent Runtime Governance Race Just Became an Infrastructure War
SAP Sapphire and Red Hat Summit both landed this week with NVIDIA OpenShell at the center of their agent architectures. When the same runtime sandbox shows up in 17 enterprise stacks simultaneously, that's not adoption — it's standardization, and it reshapes how you design production agent systems.

Table of Contents
Two major enterprise conferences happened this week. SAP Sapphire wrapped in Orlando with a keynote about the “autonomous enterprise.” Red Hat Summit ran in Boston with a platform release around agentic AI governance. Both events produced a lot of press releases and a lot of slides with the word “autonomous” on them.
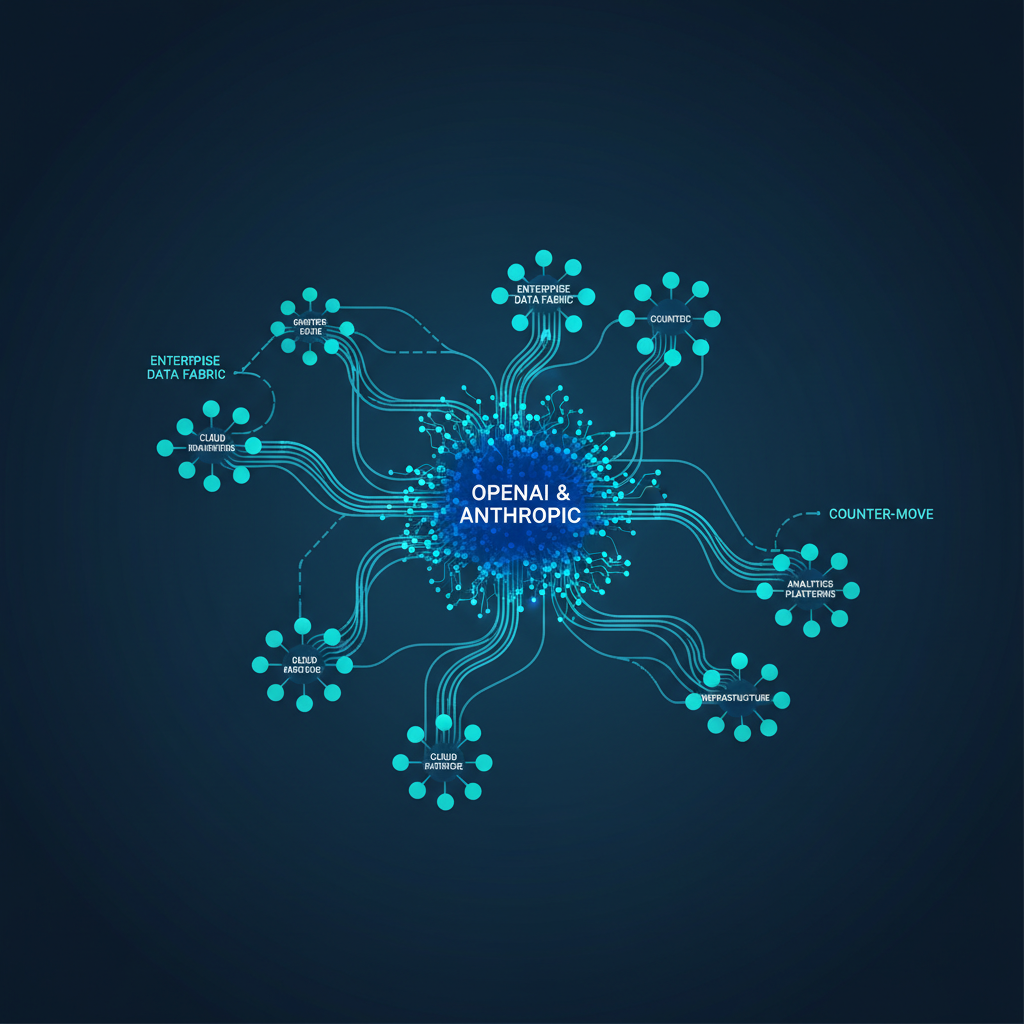
But strip away the conference theater and one technical fact stands out: NVIDIA OpenShell appeared, in a meaningful production capacity, in both announcements — and in 15 other enterprise platform stacks, for a total of 17 significant adopters in a matter of weeks. SAP is embedding OpenShell directly into Joule Studio, its agentic development runtime. Red Hat is integrating it into Red Hat AI 3.4 alongside its new AgentOps toolchain and Model-as-a-Service layer. The other 15 include Adobe, Atlassian, Salesforce, ServiceNow, Cisco, and CrowdStrike.
When a runtime sandbox lands in 17 enterprise stacks simultaneously, that is not product adoption. That is standardization. And it has direct consequences for how production agent systems need to be architected — not someday, but in the next design review cycle.
What OpenShell Actually Does (and What It Doesn’t)
Before getting into what this convergence means, it’s worth being precise about what OpenShell is, because the marketing around it has been vague in ways that matter operationally.
OpenShell is an open-source runtime that provides isolated execution environments for autonomous AI agents. Specifically, it enforces policy at the filesystem and network layers, which means it can answer the question “can this action safely execute?” at the infrastructure level rather than relying on the model’s own judgment or application-layer guardrails. Each agent runs inside a sandboxed environment with configurable policies governing what it can read, write, network to, and modify.
What OpenShell does not do is decide whether an action should happen. That is application logic — it belongs to the orchestration layer above OpenShell. SAP’s framing of this is actually quite clean: “OpenShell answers ‘can this action safely execute?’; Joule Studio runtime answers ‘should this action happen at all?’” That’s a proper separation of concerns, and it’s the right layering model if you’re building agents that touch production enterprise data.
The underlying architecture in OpenShell involves filesystem-layer containment (preventing agents from reading or writing outside their designated scope), network-layer policy (blocking or permitting egress to external endpoints at the infrastructure level), and cryptographic identity for agent processes. None of this is novel in isolation — containerization has had these primitives for years — but the combination targeted specifically at LLM agent workloads, with hooks designed for agent-framework integration, is the meaningful piece.
Red Hat’s integration in AI 3.4 takes this a layer further. The llm-d distributed inference component, combined with AgentOps (which provides tracing, observability, and lifecycle management across agent frameworks), creates what Red Hat is calling a “metal-to-agents” stack. Model-as-a-Service sits in the middle as the governed access layer — administrators define which models agents can call, with consumption tracking and policy enforcement built in. OpenShell is the execution sandbox at the base of that stack.
Why 17 Stacks in One Week Changes the Architecture Conversation
The previous state of enterprise agent deployment looked like this: each team building agents was also responsible for building their own runtime governance. Application-layer guardrails. Custom policy enforcement. Prompt-level restrictions. The result was predictably inconsistent — some teams had tight controls, others had almost none, and the gap between them wasn’t visible until something went wrong in production.
The pattern emerging from this week’s announcements is that the industry is converging on the idea that runtime governance should be an infrastructure concern, not an application concern. That is a meaningful architectural shift. It parallels how the industry eventually decided that network security shouldn’t be implemented in application code, or that secrets management shouldn’t live in config files.
The analogy worth sitting with: OpenShell to agent runtimes is what Kubernetes security contexts are to containerized workloads. You don’t trust the application to enforce its own resource limits. You enforce them at the platform layer, and the application operates within those constraints. The fact that 17 significant enterprise platforms are converging on the same runtime sandbox in the same month suggests the industry has reached a tipping point on this design principle.
This creates a near-term procurement and architecture reality. If SAP’s Joule agents and Salesforce’s agents and ServiceNow’s agents are all running in OpenShell-sandboxed environments, then your multi-vendor agent orchestration topology now has a common runtime primitive. That opens the door to policy portability — writing governance rules once and applying them across vendor boundaries. It also means your security team’s agent audit scope has a common attack surface to assess rather than 17 different black boxes.
The SuperML Take
The honest version of what happened this week is not “NVIDIA launched an agent runtime and everyone adopted it.” It’s more complicated and more interesting than that. OpenShell has been in development since at least GTC 2026 in March, and the ecosystem it landed in didn’t happen organically — Jensen Huang and SAP CEO Bill McDermott apparently worked this partnership directly, which tells you something about the strategic weight NVIDIA is putting on owning the enterprise agent execution layer.
NVIDIA’s historical playbook is worth keeping in mind here. They don’t just sell hardware. They build software ecosystems that make their hardware the natural substrate for whatever workload is hot. CUDA locked in GPU compute for ML training. Dynamo positioned them for inference orchestration. OpenShell is the bet on agent governance. Each layer up the stack increases switching cost and pulls demand for NVIDIA compute.
For enterprise AI architects, the critical question is not whether OpenShell is technically good — it appears to be reasonably well-designed. The question is what you’re signing up for when OpenShell becomes a required dependency in your agent stack. Vendor lock-in in the compute layer is one thing; vendor lock-in in the governance layer is another, because governance policies are not easily portable if you ever need to swap the runtime.
The MIT license on OpenShell is real, and NVIDIA’s contributions to the open-source codebase are genuine — SAP’s engineers are co-contributing to the codebase, which is a good sign for durability. But governance is often where open-source projects quietly add enterprise features that require vendor support agreements to operate at scale. Watch that boundary carefully over the next 12 months.
The production-ready version of the OpenShell story — distinct from the press-release version — requires answering a set of questions that neither SAP nor Red Hat addressed this week: How do you handle OpenShell policy version drift across a heterogeneous multi-vendor agent deployment? What happens when an agent’s legitimate workflow requires filesystem or network access that the current policy blocks? Who manages the policy lifecycle across teams? How does OpenShell interact with existing zero-trust frameworks? These are operational questions, not architectural ones, and they will surface in the first six months of real enterprise deployment.
For a senior platform engineer, the right move right now is to treat OpenShell as a strong candidate for your agent execution layer, run a proof-of-concept against your most security-sensitive agent workflow, and evaluate the operational surface area before committing it to your production stack. Don’t wait until your ERP vendor makes it non-optional.
Architecture Impact
What changes in system design? Agent runtime governance moves from application layer (prompt-level restrictions, model-level guardrails) to infrastructure layer (filesystem and network policy enforcement at the process level). This means your agent orchestration architecture needs to account for a new policy plane between the model serving layer and the application layer. Governance rules that were previously embedded in agent prompts or application logic need to be re-expressed as OpenShell policies, which have different semantics and different management lifecycles. Multi-vendor agent topologies gain a common execution primitive, which enables policy portability but also creates a shared failure domain.
What new failure mode appears? Over-restrictive OpenShell policies silently break agent workflows without surfacing clear error signals to the orchestration layer. An agent that can’t write to a required path or reach a required endpoint fails in ways that look like model errors, tool-use failures, or network timeouts — not policy violations — unless the observability layer is explicitly instrumented to surface OpenShell containment events. This is the agent equivalent of a firewall rule that blocks production traffic: silent, hard to diagnose, and expensive in compute spend on retried failed agentic loops.
What enterprise teams should evaluate:
- Platform engineering teams: Assess OpenShell’s policy language against your existing zero-trust framework. Determine whether you can express your current data access controls as OpenShell policies without creating gaps, and identify which of your vendor platforms are already embedding OpenShell vs. those that are not.
- Security architecture teams: Map your agent threat model against OpenShell’s actual containment boundaries. Filesystem and network isolation are strong, but OpenShell does not prevent prompt injection, model output manipulation, or application-layer business logic exploits — those require separate defense layers above the runtime.
- ML infrastructure and MLOps teams: If you’re running Red Hat AI 3.4 or planning to, evaluate the AgentOps tracing integration against your existing observability stack (Datadog, Grafana, OpenTelemetry). Determine whether llm-d distributed inference meets your latency and throughput requirements before committing to the MaaS governance model, since the two are tightly coupled in the Red Hat architecture.
- Procurement and vendor management: Audit which of your existing enterprise SaaS vendors (SAP, Salesforce, ServiceNow, Atlassian, Adobe) are embedding OpenShell, and model the governance dependency this creates. If OpenShell becomes non-optional in three or more vendor stacks, your enterprise governance policy effectively becomes a de facto NVIDIA dependency.
Cost / latency / governance / reliability implications: OpenShell adds a containment layer to every agent tool call, and the overhead is non-trivial at scale. Early benchmarks suggest policy evaluation adds roughly 2–8ms per tool invocation depending on policy complexity and filesystem scope — negligible for single-turn interactions, but meaningful for long-running agentic workflows with hundreds of tool calls per session. Governance-side, the benefit is clear: a single policy plane across multiple vendor agent environments reduces audit surface area and simplifies compliance documentation for frameworks like SR 26-2 and EU AI Act Article 13 transparency requirements. Reliability risk centers on policy drift — as agent workflows evolve and require new resource access, policy updates that lag workflow changes will silently degrade agent performance.
What to Watch
OpenShell policy portability tooling: NVIDIA and the community contributors need to ship policy management tooling — versioning, diffing, deployment pipelines — before enterprise teams can operate OpenShell at scale. Watch the GitHub repo for contribution velocity and whether any enterprise-focused policy management tools emerge in Q3 2026.
Red Hat AI 3.4 MaaS adoption: Model-as-a-Service as a governed inference layer is the right architectural move, but it requires your platform team to run and maintain the gateway. Watch whether Red Hat ships a fully managed cloud offering or keeps this as an on-premises/self-managed deployment only — that distinction determines whether MaaS is viable for mid-market enterprises without large infrastructure teams.
Non-NVIDIA runtime alternatives: The 17-stack OpenShell adoption makes it the de facto standard today, but standards attract competition. Watch whether AWS (which already has agent sandboxing in Amazon Bedrock Guardrails), Google DeepMind (Vertex AI agent governance), or an open-source community project emerges as a credible alternative runtime. The governance layer is too strategically valuable for NVIDIA to own unchallenged.
SAP Joule agent incident cases: SAP’s 50+ domain-specific Joule agents running on OpenShell in finance, supply chain, and procurement create the first large-scale real-world test of agentic AI in ERP environments. Watch for post-incident analyses and community discussions around where OpenShell containment failed or succeeded in production conditions — those will be the most honest signal about where the runtime is actually mature.
Sources
- SAP Unveils the Autonomous Enterprise | SAP Sapphire
- Shaping the Future of Secure AI Agents: How SAP and NVIDIA Are Co-Defining Enterprise-Grade Agent Execution
- SAP Embeds NVIDIA OpenShell Into Business AI Platform to Secure Enterprise AI Agents
- Red Hat Unites Builders and Operators on the Agentic Future with Major Advancements to Red Hat AI
- From inference to agents: Scaling AI in the enterprise with Red Hat AI 3.4
- Enterprise AI infrastructure modernization is now urgent | SiliconANGLE
- OpenShell Redraws the Agent Control Plane | Futurum
- Jensen Huang and Bill McDermott bet on OpenShell to secure enterprise AI agents | The New Stack
- NVIDIA Ignites the Next Industrial Revolution in Knowledge Work With Open Agent Development Platform | NVIDIA Newsroom
- Announcing New Joule Studio for Enterprise Scale Agentic Development | SAP
- Red Hat is betting on AgentOps to close the gap between AI experiments and production | The New Stack
- SAP and Anthropic: Claude on SAP Business AI Platform | SAP Sapphire
Enterprise AI Architecture
Want more enterprise AI architecture breakdowns?
Subscribe to SuperML.